 As the world continues to swap paper for screens, the amount of work completed digitally from start to finish is rising.
As the world continues to swap paper for screens, the amount of work completed digitally from start to finish is rising.
Construction companies perpetuate this trend with the use of digital applications for project management, communication, virtual design and construction and various support services. With so many critical processes online, safeguarding information in endless password-protected environments should be simple, right?
Unfortunately, hackers are getting more creative in how they access your information. In some ways, their efforts are technically more sophisticated, in other ways, they’re learning how to better appeal to gatekeepers. The unparalleled convenience of digital also comes with great responsibility, as many devices are tied directly to larger networks and other constituents. The good news is that there are a variety of ways users can protect themselves when they’re armed with knowledge.
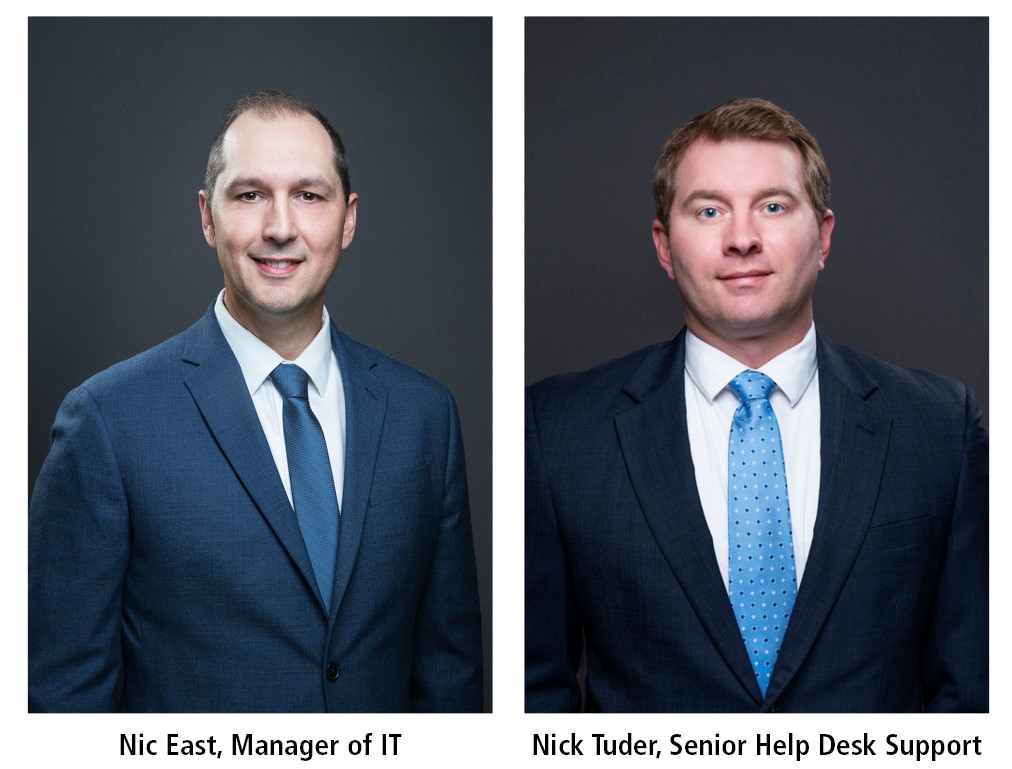
To get a better grasp of some of the ways to be safer in conducting business in a connected environment, we sat down for a quick chat with Robins & Morton’s Manager of Information Technology, Nic East, and Senior HelpDesk Support, Nick Tuder.
Q: With the construction industry moving toward a more paperless approach, how important is cyber security to employees working both inside and outside of information technology?
A, Nick Tuder: As we process more documents electronically, security will play a significant role in how we transfer those documents between employees. Not only do the documents need to be securely stored, they also need to be securely sent. Hackers understand that people are using more electronic methods to share files and they latch onto those processes, finding ways to exploit them. This happened with DocuSign recently. Users received an email asking them to open an attachment, and it ultimately installed malware on their workstation.
Q: What is the most common entryway for hackers?
A, Nic East: The most common entryway for hackers is through the end user. Unfortunately, you can have all the security that you need sitting at the perimeter of the network, but all it takes is one person to open the door and let the hackers in. This can happen by clicking on a link or opening an infected attachment.
Q: In what ways can your information be targeted on web-based applications?
A, Nick Tuder: Web-based applications, especially public-facing websites, create avenues for hackers to learn about you and find ways to trick you into clicking on something. This is called social engineering. Imagine that I state that I’m an Excel expert on my bio page. A hacker could then disguise themselves as an internal employee and send me an exploited Excel file, asking for some help with their document. That Excel file could then open a door into our company and allow them to steal or corrupt data.
Q: How can you keep your apps safe?
A, Nic East: Fortunately, there are many ways to keep apps safe. First, keep them up to date. Second, apps should only be installed from trusted sources. Third, enabling two-factor authentication when available will help provide an additional layer of security. Also, remember to remove old apps that you don’t use anymore. Sometimes, an app will be forgotten by the developer, meaning that developer has not patched the app, so it could open up security holes on your device.
Q: When a website, application, etc. is “hacked,” what’s the goal of the hacker, typically?
A, Nick Tuder: Most hackers are looking for monetary gain. The purpose of hacking could be to open a door into your network to steal data and sell it on the Dark Web. It could also be to hold your files hostage until you pay a fee. Other times, more uncommonly, it is just a method to cause chaos and panic – think about someone just changing your website to something funny or malicious.
Q: What are some of the terms to know in reference to cyber security?
- Phishing – This is when you get an email that has either a link or a bad attachment. The goal of phishing is to get you to enter your credentials or other personal information.
- Spear Phishing – Almost like regular phishing, but it is targeted to individuals in higher-ranking positions.
- Data Breach – This happens when a company’s network is attacked and valuable information is stolen. Sometimes, this can be as simple as usernames and email addresses. Other times, it can include credit cards and other personal information.
- Ransomware – This is software that takes hold of your system and locks your files. Trying to access the locked files triggers a note that claims you are locked out of your files until you pay a ransom – averaging more than $600.
- Spyware – This software that is installed on your computer that allows hackers to spy on you. They can collect your key strokes, which in turn allow them to determine your passwords and credit card numbers.
Q: What kinds of threats do you see growing in the cyber security realm?
A, Nic East: Cybersecurity is one of the fastest growing sectors of information technology right now, because hackers are constantly getting better and learning new ways to get into networks. We have to constantly stay on our toes. A few growing areas of attack include:
- The rise of state-sponsored attacks – This is possibly one of the most concerning areas of attack. These attacks are politically motivated and go beyond financial gain. Basically, this kind of attack is when a government hires teams of hackers to infiltrate another country’s government. This can attack basic infrastructures like power grids and water systems.
- Internet of Things (IoT) devices and ransomware – While it’s unlikely that a hacker would target your smart refrigerator at your house, connecting devices to the internet can be a larger upcoming problem. As more devices connect to the internet, they become targets to hackers. As these devices are sometimes not made by reputable vendors, they could open holes that would allow a hacker to get into your network, steal data or hold it ransom.
- AI-powered attacks – Artificial Intelligence, or Machine Learning Software, allows a computer to “learn” from the consequences of past events in order to predict cybersecurity events and prevent them. However, good always comes with evil. AI can be used to assist hackers when it comes to cracking your password.
Q: What trends do you see growing in companies to prevent cyber security crime?
A, Nick Tuder: The biggest threat to a company is end-user threat. This can come from someone clicking on a link and entering their password or someone opening a bad attachment. The best way to address this is end-user training. When an employee is trained on what to look for, they are better prepared when they get into one of these situations. Another way is two-factor authentication. The first factor is your password. That’s something you know. The second factor is your cell phone. That’s something you have. With these combined factors, your account is much harder to hack, as the hacker would need direct access to your phone.
Q: With all kinds of new scams through email, smartphones, and web apps – what are signs that an illegitimate source is trying to gather your information?
A, Nick Tuder: This is where training will come into play. Typically, you wouldn’t be able to tell when a hacker is in your system, however if you know what to look for on the front end, you might be able to prevent that hacker from getting in. The only true way to prevent hackers from infiltrating your system is to be skeptical. Look at a link before you click it. If someone sent it to you, you should ask yourself if this person meant to sent you the link. Maybe reach out to them in another email to ask if they did. Another method might be to look at the email return address. Does it match the syntax of the person you know? Meaning, does it have the correct name@domain.com. Also, look at the language of the email. Do the sentences look like they were translated? There are other things to look for, but training is one of the best ways to prevent an attack.
Q: How important is backing up information in case of cyber attack and what is the best avenue for that?
A, Nic East: Performing backups is the number one way to get your files back, should there be an attack. Backups are the most important part of a company’s system. To add to that, the backups should be stored in an offline device. One of the first things ransomware looks for is a copy of your backups. If it’s directly attached to your device, that will be one of the first places the software looks. Backup your device, then unplug the device and store it safely. Hackers can’t attack something that isn’t powered on.
Q: How can members of an organization help prevent security breakdown?
A, Nick Tuder: Security is everyone’s job. All it takes is one click and everything could be compromised. That’s a bit of a scare-tactic, but it’s very important that everyone in the organization understands their role in keeping the company safe. When it doubt, reach out to the information technology department and ask about something suspicious. We have the training to spot things that most people might not see.
Q: If you are a victim of a cyber crime, what should you do?
A, Nic East: The Internet Crime Complaint Center is a public-facing division of the FBI. You can go to https://www.ic3.gov, if you feel like you were a victim. The FBI will take action to try to catch the offender. In your organization, you must reach out to the information technology department, if you believe you have been compromised. If you delay, there could be catastrophic results from the attack.

